A Linux administrator would like to use systemd to schedule a job to run every two hours. The administrator creates timer and service definitions and restarts the server to load these new configurations. After the restart, the administrator checks the log file and notices that the job is only running daily. Which of the following is MOST likely causing the issue?
A systems administrator wants to permit access temporarily to an application running on port 1234/TCP on a Linux server. Which of the following commands will permit this traffic?
The security team has identified a web service that is running with elevated privileges A Linux administrator is working to change the systemd service file to meet security compliance standards. Given the following output:
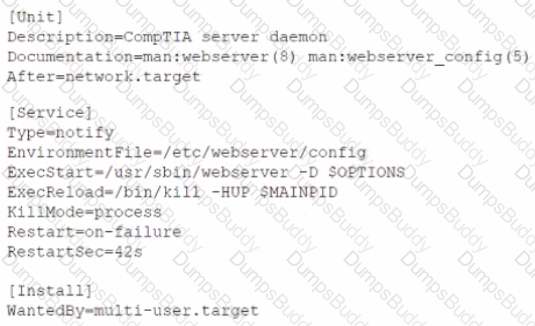
Which of the following remediation steps will prevent the web service from running as a privileged user?
A Linux systems administrator is updating code. After completing the update, the administrator wants to publish the updated code without including the configuration files. Which of the following should the administrator use to accomplish this task?
A systems administrator is tasked with changing the default shell of a system account in order to disable iterative logins. Which of the following is the
best option for the administrator to use as the new shell?
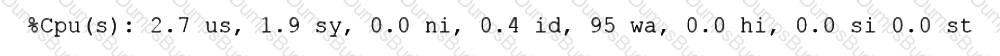
A systems administrator is deploying three identical, cloud-based servers. The administrator is using the following code to complete the task:
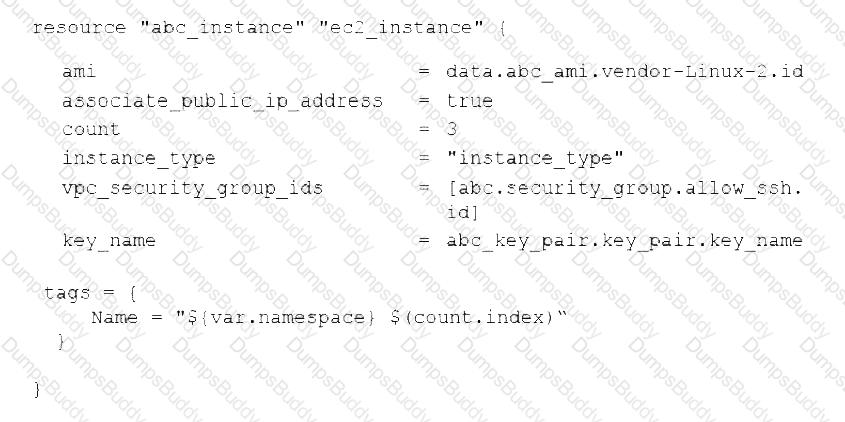
Which of the following technologies is the administrator using?
A technician just fixed a few issues in some code and is ready to deploy the code into production. Which of the following steps should the technician take next?
A systems administrator made some unapproved changes prior to leaving the company. The newly hired administrator has been tasked with revealing the system to a compliant state. Which of the following commands will list and remove the correspondent packages?
A Linux systems administrator receives a notification that one of the server’s filesystems is full. Which of the following commands would help the administrator to identify this filesystem?
A non-privileged user is attempting to use commands that require elevated account permissions, but the commands are not successful. Which of the following most likely needs to be updated?
An administrator installed an application from source into /opt/operations1/ and has received numerous reports that users are not able to access the application without having to use the full path /opt/operations1/bin/*. Which of the following commands should be used to resolve this issue?
A Linux administrator is alerted to a storage capacity issue on a server without a specific mount point or directory. Which of the following commands would be MOST helpful for troubleshooting? (Choose two.)
A Linux administrator modified the SSH configuration file. Which of the following commands should be used to apply the configuration changes?
A systems administrator made some changes in the ~/.bashrc file and added an alias command. When the administrator tried to use the alias command, it did not work. Which of the following should be executed FIRST?
An application developer received a file with the following content:
##This is a sample Image ##
FROM ubuntu:18.04
MAINTAINER demohut@gtmail.com.hac
COPY . /app
RUN make /app
CMD python /app/app.py
RUN apt-get update
RUN apt-get install -y nginx
CMD ["echo","Image created"]
The developer must use this information to create a test bed environment and identify the image (myimage) as the first version for testing a new
application before moving it to production. Which of the following commands will accomplish this task?
A Linux administrator needs to transfer a local file named accounts . pdf to a remote / tmp directory of a server with the IP address 10.10.10.80. Which of the following commands needs to be executed to transfer this file?
An administrator changed the default port of an SSH server to 2222 on myhost, and clients are not able to connect. The administrator runs some commands and receives the following output:
vbnet
Copy code
$ ssh -p 2222 myhost
ssh:connect to host myhost on port 2222: No route to host
Which of the following commands should be run on myhost?
A Linux administrator needs to create a symlink for /usr/local/bin/app-a, which was installed in /usr/local/share/app-a. Which of the following commands should the administrator use?
The journald entries have filled a Linux machine’s /var volume. Which of the following is the best command for a systems administrator to use to free up the disk space occupied by these entries?
The development team created a new branch with code changes that a Linux administrator needs to pull from the remote repository. When the administrator looks for the branch in Git, the branch in question is not visible. Which of the following commands should the Linux administrator run to refresh the branch information?
In order to copy data from another VLAN, a systems administrator wants to temporarily assign IP address 10.0.6 5/24 to the newly added network interface enp1s0f1. Which of the following commands should the administrator run to achieve the goal?
A systems administrator has been unable to terminate a process. Which of the following should the administrator use to forcibly stop the process?
A junior developer is unable to access an application server and receives the following output:
The systems administrator investigates the issue and receives the following output:
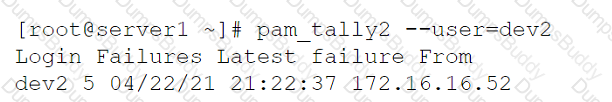
Which of the following commands will help unlock the account?
An administrator attempts to connect to a remote server by running the following command:
$ nmap 192.168.10.36
Starting Nmap 7.60 ( https://nmap.org ) at 2022-03-29 20:20 UTC
Nmap scan report for www1 (192.168.10.36)
Host is up (0.000091s latency).
Not shown: 979 closed ports
PORT STATE SERVICE
21/tcp open ftp
22/tcp filtered ssh
631/tcp open ipp
Nmap done: 1 IP address (1 host up) scanned in 0.06 seconds
Which of the following can be said about the remote server?
Which of the following would significantly help to reduce data loss if more than one drive fails at the same time?
A Linux engineer finds multiple failed login entries in the security log file for application users. The Linux engineer performs a security audit and discovers a security issue. Given the following:
# grep -iE '*www*|db' /etc/passwd
www-data:x:502:502:www-data:/var/www:/bin/bash
db:x: 505:505:db: /opt/db:/bin/bash
Which of the following commands would resolve the security issue?
Which of the following commands should a technician use to create an administrative account for the username Joe?
A cloud engineer needs to change the secure remote login port from 22 to 49000. Which of the following files should the engineer modify to change the port number to the desired value?
Due to low disk space, a Linux administrator finding and removing all log files that were modified more than 180 days ago. Which of the following commands will accomplish this task?
A systems administrator wants to back up the directory /data and all its contents to /backup/data on a remote server named remote. Which of the following commands will achieve the desired effect?
A junior administrator is setting up a new Linux server that is intended to be used as a router at a remote site. Which of the following parameters will accomplish this goal?
A Linux administrator recently downloaded a software package that is currently in a compressed file. Which of the following commands will extract the files?
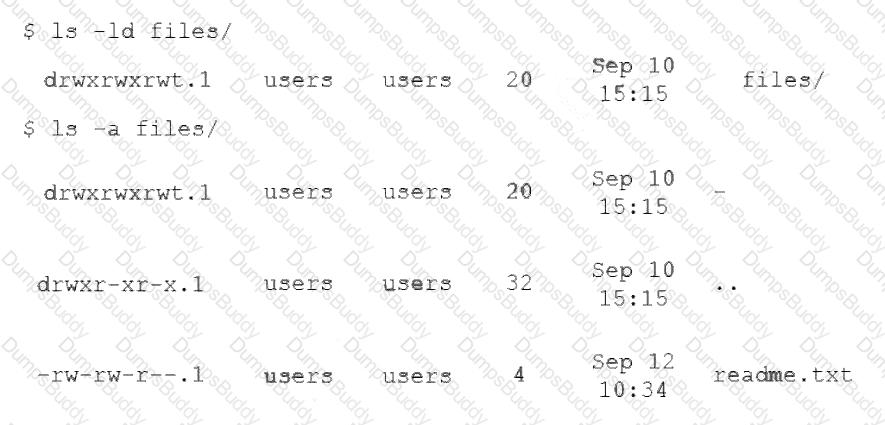
A Linux administrator wants a permission bit on a shared folder that allows only the owner of the file within that directory or the root user to delete or rename the file. Which of the following commands will help achieve this goal?
A systems administrator checked out the code from the repository, created a new branch, made changes to the code, and then updated the main branch. The systems administrator wants to ensure that the Terraform state files do not appear in the main branch. Which of following should the administrator use to meet this requirement?
A Linux administrator needs to harden a system and guarantee that the Postfix service will not run, even after a restart or system upgrade. Which of the following commands allows the administrator to fulfill the requirement?
A systems administrator is troubleshooting a connectivity issue pertaining to access to a system named db.example.com. The system IP address should be 192.168.20.88. The administrator issues the dig command and receives the following output:
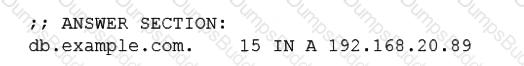
The administrator runs grep db.example.com /etc/hosts and receives the following output:
Given this scenario, which of the following should the administrator do to address this issue?
A server is experiencing intermittent connection issues. Some connections to the Internet work as intended, but some fail as if there is no connectivity. The systems administrator inspects the server configuration:

Which of the following is MOST likely the cause of the issue?
A Linux administrator provisioned a new web server with custom administrative permissions for certain users. The administrator receives a report that user1 is unable to restart the Apache web service on this server. The administrator reviews the following output:
[ root@server ] # id user1
UID=1011 (user1) gid=1011 (USER1) groups=1011 (user1), 101 (www-data), 1120 (webadmin)
[ root@server ] # cat /etc/sudoers.d/custom.conf
user1 ALL=/usr/sbin/systemctl start httpd, /usr/sbin/systemctl stop httpd
webadmin ALL=NOPASSWD: /etc/init.d.httpd restart, /sbin/service httpd restart, /usr/sbin/apache2ctl restart
#%wheel ALL=(ALL) NOPASSWD: ALL
Which of the following would most likely resolve the issue while maintaining a least privilege security model?
A Linux systems administrator needs to compress a file named passwords.txt. The compressed file should be saved as passwords.txt.gz. Which of the following commands should the administrator use to accomplish this task?
A Linux administrator created the directory /project/access2all. By creating this directory, the administrator is trying to avoid the deletion or modification of files from non-owners. Which of the following will accomplish this goal?
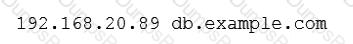
A Linux administrator has installed a web server, a database server, and a web application on a server. The web application should be active in order to render the web pages. After the administrator restarts the server, the website displays the following message in the browser: Error establishing a database connection. The Linux administrator reviews the following relevant output from the systemd init files:
The administrator needs to ensure that the database is available before the web application is started. Which of the following should the administrator add to the HTTP server .service file to accomplish this task?
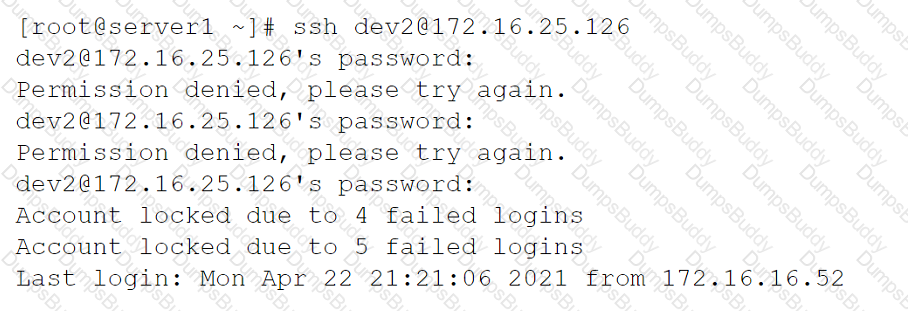
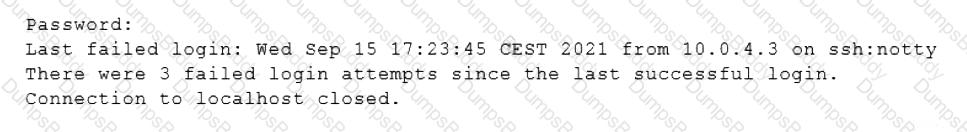
A user reported issues when trying to log in to a Linux server. The following outputs were received:
Given the outputs above. which of the following is the reason the user is una-ble to log in to the server?
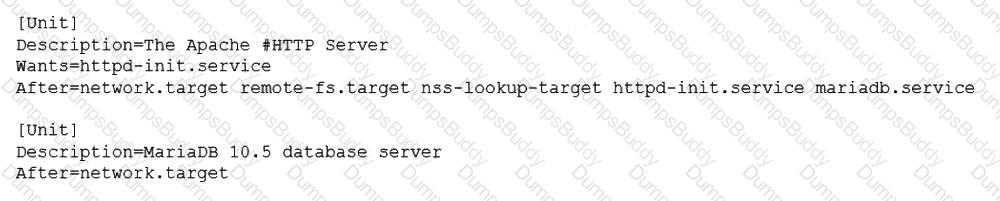
A junior Linux administrator is tasked with installing an application. The installation guide states the application should only be installed in a run level 5 environment.
Which of the following commands would ensure the server is set to runlevel 5?
A systems administrator identifies multiple processes in a zombie state. Which of the following signals would be best for the administrator to send to the PPID?
A cloud engineer needs to launch a container named web-01 in background mode. Which of the following commands will accomplish this task''
A DevOps engineer is working on a local copy of a Git repository. The engineer would like to switch from the main branch to the staging branch but notices the staging branch does not exist. Which of the following Git commands should the engineer use to perform this task?
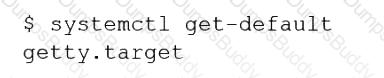
A Linux administrator booted up the server and was presented with a non-GUI terminal. The administrator ran the command systemct1 isolate graphical.target and rebooted the system by running systemct1 reboot, which fixed the issue. However, the next day the administrator was presented again with a non-GUI terminal. Which of the following is the issue?
A Linux administrator has defined a systemd script docker-repository.mount to mount a volume for use by the Docker service. The administrator wants to ensure that the Docker service does not start until the volume is mounted. Which of the following configurations needs to be added to the Docker service definition to best accomplish this task?
A Linux administrator is trying to start the database service on a Linux server but is not able to run it. The administrator executes a few commands and receives the following output:
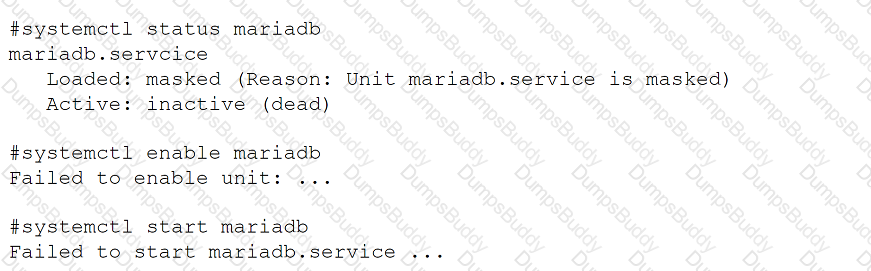
Which of the following should the administrator run to resolve this issue? (Select two).
A Linux administrator intends to start using KVM on a Linux server. Which of the following commands will allow the administrator to load the KVM module as
well as any related dependencies?
A DevOps engineer needs to allow incoming traffic to ports in the range of 4000 to 5000 on a Linux server. Which of the following commands will enforce this rule?
An operations engineer is planning to start a container running a PostgreSQL database. The engineer wants the container to start automatically at system startup, mount the /home/db directory as /var/lib/postgresql inside the container, and expose port 5432 to the OS. Which of the following commands should the engineer run to achieve this task?
Following the migration from a disaster recovery site, a systems administrator wants a server to require a user to change credentials at initial login. Which of the following commands should
be used to ensure the aging attribute?
A Linux administrator is tasked with adding users to the system. However, the administrator wants to ensure the users’ access will be disabled once the project is over. The expiration date should be 2021-09-30. Which of the following commands will accomplish this task?
A Linux administrator created a new file system. Which of the following files must be updated to ensure the filesystem mounts at boot time?
A Linux administrator reviews a set of log output files and needs to identify files that contain any occurrence of the word denied. All log files containing entries in uppercase or lowercase letters should be included in the list. Which of the following commands should the administrator use to accomplish this task?
A systems administrator created a new Docker image called test. After building the image, the administrator forgot to version the release. Which of the following will allow the administrator to assign the v1 version to the image?
A systems administrator configured firewall rules using firewalld. However, after the system is rebooted, the firewall rules are not present:

The systems administrator makes additional checks:
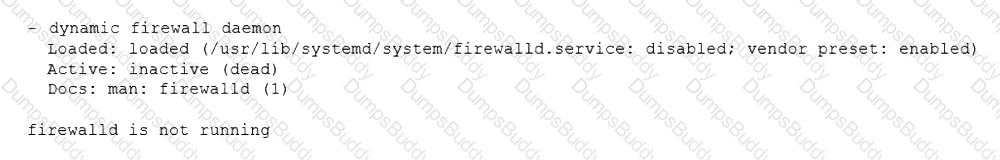
Which of the following is the reason the firewall rules are not active?
A Linux administrator has logged in to a server for the first time and needs to know which services are allowed through the firewall. Which of the following options will return the results for which the administrator is looking?
A Linux administrator needs to obtain a list of all volumes that are part of a volume group. Which of the following commands should the administrator use to accomplish this task?
A Linux administrator needs to remove all local firewall rules on a Linux system. Which of the following commands should the administrator run?
A Linux systems administrator is trying to execute a particular shell script on a server. The administrator reviews the following outputs:
shell
$ ./startup.sh
bash: ./startup.sh: Permission denied
$ ls -l startup.sh
-rw-rw-r-- 1 companyabc companyabc 18 October 15:35 startup.sh
Which of the following commands should the administrator use to allow the script to run?
Users are experiencing high latency when accessing a web application served by a Linux machine. A systems administrator checks the network interface counters and sees the following:

Which of the following is the most probable cause of the observed latency?
A systems administrator receives reports that several virtual machines in a host are responding slower than expected. Upon further investigation, the administrator obtains the following output from one of the affected systems:
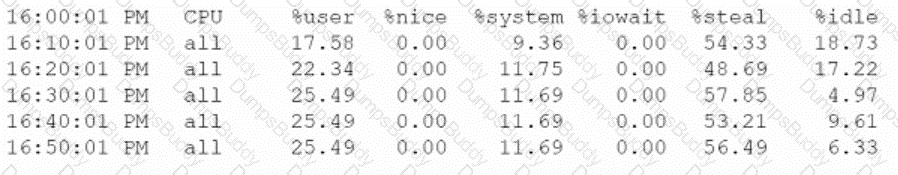
Which of the following best explains the reported issue?
While troubleshooting server issues, a Linux systems administrator obtains the following output:
yaml
total used free shared buff/cache available
Mem: 3736 3538 33 2 48 25
Swap: 2047 1824 223
Which of the following best describes the state of the system?
A cloud engineer needs to block the IP address 192.168.10.50 from accessing a Linux server. Which of the following commands will achieve this goal?
A systems administrator is working on a security report from the Linux servers. Which of the following commands can the administrator use to display all the firewall rules applied to the Linux servers? (Select two).
A Linux system is failing to start due to issues with several critical system processes. Which of the following options can be used to boot the system into the single user mode? (Choose two.)
A systems administrator intends to use a UI-JID to mount a new partition per-manently on a Linux system. Which of the following commands can the adminis-trator run to obtain information about the UUlDs of all disks attached to a Linux system?
A Linux administrator wants to set the SUID of a file named dev_team.text with 744 access rights. Which of the following commands will achieve this goal?
A systems administrator is troubleshooting connectivity issues and trying to find out why a Linux server is not able to reach other servers on the same subnet it is connected to. When listing link parameters, the following is presented:
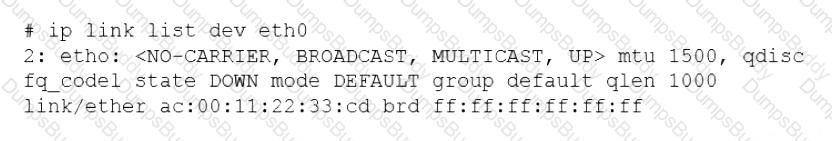
Based on the output above, which of following is the MOST probable cause of the issue?
Which of the following specifications is used to perform disk encryption in a Linux system?
A developer reported an incident involving the application configuration file /etc/httpd/conf/httpd.conf that is missing from the server. Which of the following identifies the RPM package that installed the configuration file?
A systems administrator requires that all files that are created by the user named web have read-only permissions by the owner. Which of the following commands will satisfy this requirement?
A systems administrator is investigating an issue in which one of the servers is not booting up properly. The journalctl entries show the following:
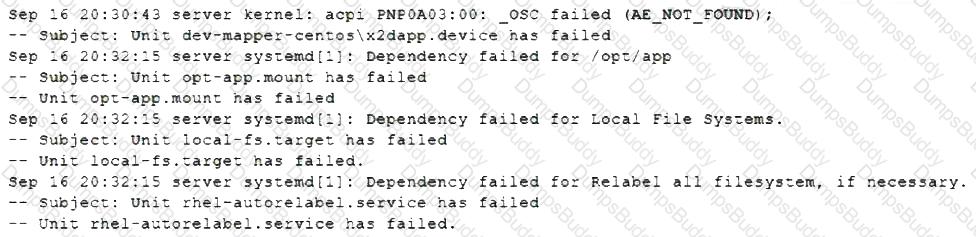
Which of the following will allow the administrator to boot the Linux system to normal mode quickly?
Users report that connections to a MariaDB service are being closed unexpectedly. A systems administrator troubleshoots the issue and finds the following message in /var/log/messages:
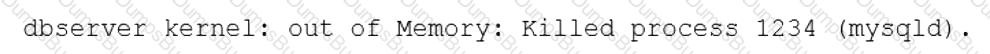
Which of the following is causing the connection issue?
A systems administrator creates a public key for authentication. Which of the following tools is most suitable to use when uploading the key to the remote
servers?
A user is cleaning up a directory because it has more than 100,000 files that were generated from an experiment. When the user tries to remove the unneeded experiment files, the user receives an error:
arduino
cannot execute [Argument list too long]
Which of the following should the user execute to remove these files?
A systems administrator is reviewing the following output on the text editor that is being used to update the company's internal database records:
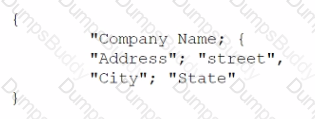
Which of the following extensions should the systems administrator use when saving the file?
An administrator attempts to rename a file on a server but receives the following error.
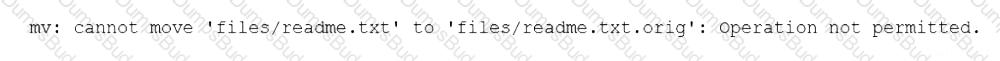
The administrator then runs a few commands and obtains the following output:
Which of the following commands should the administrator run NEXT to allow the file to be renamed by any user?
A security team discovers that a web server has been running with elevated privileges and identifies it as a security violation. Which of the following items needs to be added to the webserver.service file to remediate the issue?
A cloud engineer is installing packages during VM provisioning. Which of the following should the engineer use to accomplish this task?
A junior systems administrator has just generated public and private authentication keys for passwordless login. Which of the following files will be moved to the remote servers?
Junior system administrator had trouble installing and running an Apache web server on a Linux server. You have been tasked with installing the Apache web server on the Linux server and resolving the issue that prevented the junior administrator from running Apache.
INSTRUCTIONS
Install Apache and start the service. Verify that the Apache service is running with the defaults.
Typing “help” in the terminal will show a list of relevant event commands.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.

After connecting to a remote host via SSH, an administrator attempts to run an application but receives the following error:
arduino
Error: cannot open display:
Which of the following should the administrator do to resolve this error?
A Linux administrator needs to remove software from the server. Which of the following RPM options should be used?
A Linux administrator is implementing a stateful firewall on the Linux server. Which of the following iptables options will be required to build the stateful rules? (Select two).
When trying to log in remotely to a server, a user receives the following message:
The server administrator is investigating the issue on the server and receives the following outputs:
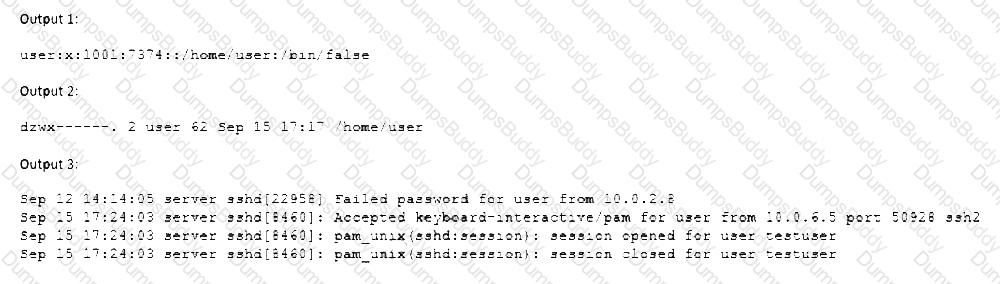
Which of the following is causing the issue?
Developers have requested implementation of a persistent, static route on the application server. Packets sent over the interface eth0 to 10.0.213.5/32 should be routed via 10.0.5.1. Which of the following commands should the administrator run to achieve this goal?
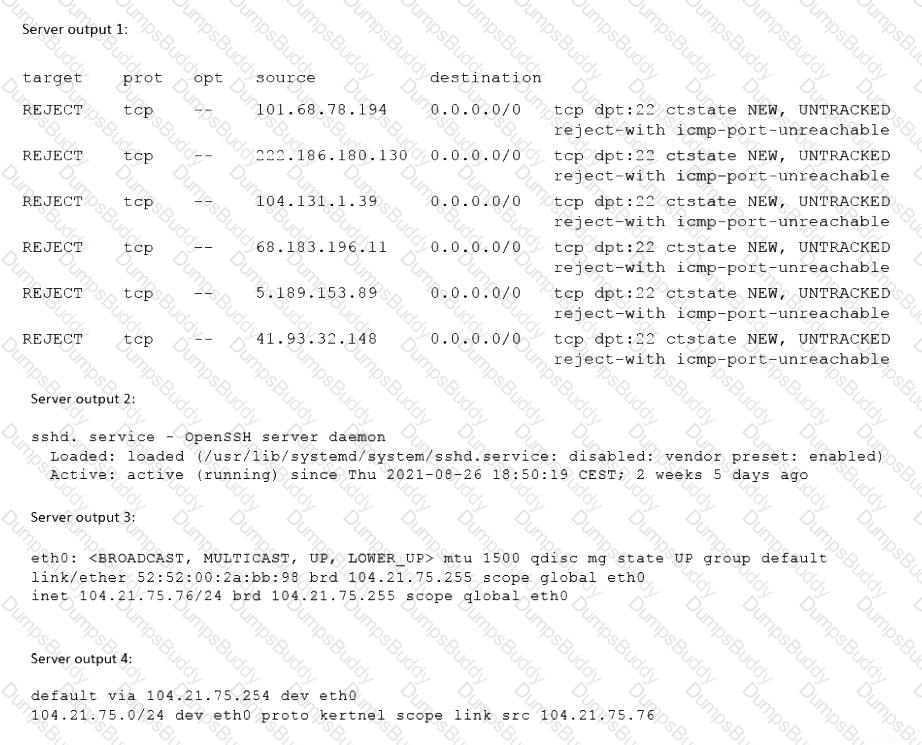
A user is unable to remotely log on to a server using the server name server1 and port 22. The Linux engineer troubleshoots the issue and gathers the following information:
Which of the following is most likely causing the issue?
A Linux administrator needs to check extended permissions applied to the directory test. Which of the following commands should the administrator use to help with this task?
A Linux administrator is trying to remove the ACL from the file /home/user/data. txt but receives the following error message:
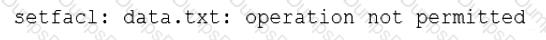
Given the following analysis:
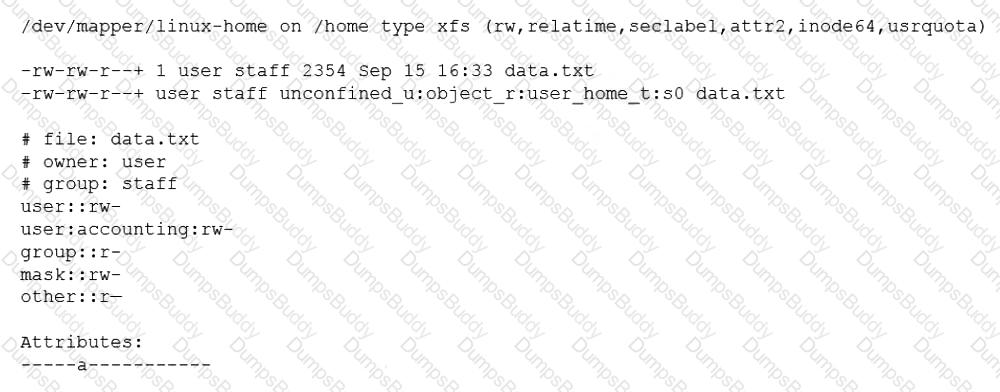
Which of the following is causing the error message?
An administrator started a long-running process in the foreground that needs to continue without interruption. Which of the following keystrokes should the administrator use to continue running the process in the background?
A Linux administrator is troubleshooting a systemd mount unit file that is not working correctly. The file contains:
[root@system] # cat mydocs.mount
[Unit]
Description=Mount point for My Documents drive
[Mount]
What=/dev/drv/disk/by-uuid/94afc9b2-ac34-ccff-88ae-297ab3c7ff34
Where=/home/user1/My Documents
Options=defaults
Type=xfs
[Install]
WantedBy=multi-user.target
The administrator verifies the drive UUID correct, and user1 confirms the drive should be mounted as My Documents in the home directory. Which of the following can the administrator
do to fix the issues with mounting the drive? (Select two).
The group named support is unable to make changes to the config file. An administrator is reviewing the permissions and sees the following:
S Is -1 config
-rw-rw----. 1 root app 4682 02-15 11:25 config
Which of the following should the administrator execute in order to give the support group access to modify the file while preserving the current ownership?
A Linux systems administrator needs to copy files and directories from Server A to Server B. Which of the following commands can be used for this purpose? (Select TWO)
A systems administrator created a new directory with specific permissions. Given the following output:
# file: comptia
# owner: root
# group: root
user: : rwx
group :: r-x
other: :---
default:user :: rwx
default:group :: r-x
default:group:wheel: rwx
default:mask :: rwx
default:other ::-
Which of the following permissions are enforced on /comptia?
A Linux administrator is troubleshooting SSH connection issues from one of the workstations.
When users attempt to log in from the workstation to a server with the IP address 104.21.75.76, they receive the following message:
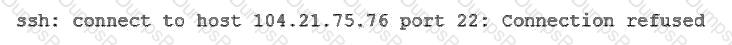
The administrator reviews the information below:
Which of the following is causing the connectivity issue?
A Linux engineer set up two local DNS servers (10.10.10.10 and 10.10.10.20) and was testing email connectivity to the local mail server using the mail command on a local machine when the following error appeared:
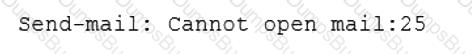
The local machine DNS settings are:
Which of the following commands could the engineer use to query the DNS server to get mail server information?
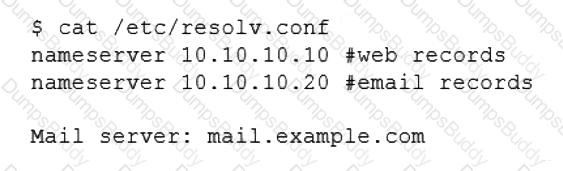
A systems administrator received a notification that a system is performing slowly. When running the top command, the systems administrator can see the following values:
Which of the following commands will the administrator most likely run NEXT?
A systems administrator received a request to change a user's credentials. Which of the following commands will grant the request?
A systems administrator is tasked with creating a cloud-based server with a public IP address.
Which of the following technologies did the systems administrator use to complete this task?
A systems administrator is installing various software packages using a pack-age manager. Which of the following commands would the administrator use on the Linux server to install the package?
A systems administrator wants to list all local account names and their respective UIDs. Which of the following commands will provide output containing this information?
An administrator thinks that a package was installed using a snap. Which of the following commands can the administrator use to verify this information?
A systems administrator created a new directory with specific permissions. Given the following output:
arduino
$ ls -ld /comptia
drwxr-x--- 2 root root 4096 Oct 20 20:13 /comptia
$ getfacl /comptia
# file: /comptia
# owner: root
# group: root
user::rwx
group::r-x
other::---
default:user::rwx
default:group::r-x
default:group:wheel:rwx
default:mask::rwx
default:other::---
Which of the following permissions are enforced on /comptia?