A company that uses VoIP telephones is experiencing intermittent issues with one-way audio and dropped conversations The manufacturer says the system will work if ping times are less than 50ms. The company has recorded the following ping times:
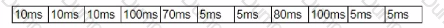
Which of the following is MOST likely causing the issue?
Which of the following is used to provide networking capability for VMs at Layer 2 of the OSI model?
A network engineer is investigating reports of poor network performance. Upon reviewing a device configuration, the engineer finds that duplex settings are mismatched on both ends. Which of the following would be the MOST likely result of this finding?
A network field technician is installing and configuring a secure wireless network. The technician performs a site survey. Which of the following documents would MOST likely be created as a result of the site survey?
A network administrator wants to improve the security of the management console on the company's switches and ensure configuration changes made can be correlated to the administrator who conformed them Which of the following should the network administrator implement?
A network administrator is required to ensure that auditors have read-only access to the system logs, while systems administrators have read and write access to the system logs, and operators have no access to the system logs. The network administrator has configured security groups for each of these functional categories. Which of the following security capabilities will allow the network administrator to maintain these permissions with the LEAST administrative effort?
There are two managed legacy switches running that cannot be replaced or upgraded. These switches do not support cryptographic functions, but they are password protected. Which of the following should a network administrator configure to BEST prevent unauthorized access?
Which of the following technologies allows traffic to be sent through two different ISPs to increase performance?
A network technician needs to correlate security events to analyze a suspected intrusion. Which of the following should the technician use?
A business is using the local cable company to provide Internet access. Which of the following types of cabling will the cable company MOST likely use from the demarcation point back to the central office?
Which of the following OSI model layers is where conversations between applications are established, coordinated, and terminated?
A small, family-run business uses a single SOHO router to provide Internet and WiFi to its employees At the start of a new week, employees come in and find their usual WiFi network is no longer available, and there is a new wireless network to which they cannot connect. Given that information, which of the following should have been done to avoid this situation'
A user recently made changes to a PC that caused it to be unable to access websites by both FQDN and IP Local resources, such as the file server remain accessible. Which of the following settings did the user MOST likely misconfigure?
A user reports a weak signal when walking 20ft (61 m) away from the WAP in one direction, but a strong signal when walking 20ft in the opposite direction The technician has reviewed the configuration and confirmed the channel type is correct There is no jitter or latency on the connection Which of the following would be the MOST likely cause of the issue?
A firewall administrator is implementing a rule that directs HTTP traffic to an internal server listening on a non-standard socket Which of the following types of rules is the administrator implementing?
A local firm has hired a consulting company to clean up its IT infrastructure. The consulting company notices remote printing is accomplished by port forwarding via publicly accessible IPs through the firm's firewall Which of the following would be the MOST appropriate way to enable secure remote printing?
A technician is connecting DSL for a new customer. After installing and connecting the on-premises equipment, the technician verifies DSL synchronization. When connecting to a workstation, however, the link LEDs on the workstation and modem do not light up. Which of the following should the technician perform during troubleshooting?
A network technician is configuring a new firewall for a company with the necessary access requirements to be allowed through the firewall. Which of the following would normally be applied as the LAST rule in the firewall?
A network administrator is downloading a large patch that will be uploaded to several enterprise switches simultaneously during the day's upgrade cycle. Which of the following should the administrator do to help ensure the upgrade process will be less likely to cause problems with the switches?
A network technician is installing an analog desk phone for a new receptionist After running a new phone line, the technician now needs to cnmp on a new connector. Which of the following connectors would MOST likely be used in this case?
A network technician is observing the behavior of an unmanaged switch when a new device is added to the network and transmits data. Which of the following BEST describes how the switch processes this information?
Which of the following protocol types describes secure communication on port 443?
Which of the following protocols will a security appliance that is correlating network events from multiple devices MOST likely rely on to receive event messages?
A city has hired a new employee who needs to be able to work when traveling at home and at the municipal sourcing of a neighboring city that snares services. The employee is issued a laptop, and a technician needs to train the employee on the appropriate solutions for secure access to the network from all the possible locations On which of the following solutions would the technician MOST likely train the employee?
A network technician is reviewing an upcoming project's requirements to implement laaS. Which of the following should the technician consider?
An ARP request is broadcasted and sends the following request.
''Who is 192.168.1.200? Tell 192.168.1.55''
At which of the following layers of the OSI model does this request operate?
A corporation has a critical system that would cause unrecoverable damage to the brand if it was taken offline. Which of the following disaster recovery solutions should the corporation implement?
A network technician is investigating an issue with a desktop that is not connecting to the network. The desktop was connecting successfully the previous day, and no changes were made to the environment. The technician locates the switchport where the device is connected and observes the LED status light on the switchport is not lit even though the desktop is turned on Other devices that arc plugged into the switch are connecting to the network successfully Which of the following is MOST likely the cause of the desktop not connecting?
Which of the following attacks encrypts user data and requires a proper backup implementation to recover?
Which of the following would be used to expedite MX record updates to authoritative NSs?
A network administrator is implementing OSPF on all of a company’s network devices. Which of the following will MOST likely replace all the company’s hubs?
A network administrator is talking to different vendors about acquiring technology to support a new project for a large company. Which of the following documents will MOST likely need to be signed before information about the project is shared?
A network administrator is reviewing interface errors on a switch. Which of the following indicates that a switchport is receiving packets in excess of the configured MTU?
A network administrator is configuring a database server and would like to ensure the database engine is listening on a certain port. Which of the following commands should the administrator use to accomplish this goal?
A network administrator is configuring a load balancer for two systems. Which of the following must the administrator configure to ensure connectivity during a failover?
A network technician is investigating an issue with handheld devices in a warehouse. Devices have not been connecting to the nearest APs, but they have been connecting to an AP on the far side of the warehouse. Which of the following is the MOST likely cause of this issue?
A wireless network was installed in a warehouse for employees to scan crates with a wireless handheld scanner. The wireless network was placed in the corner of the building near the ceiling for maximum coverage However users in the offices adjacent lo the warehouse have noticed a large amount of signal overlap from the new network Additionally warehouse employees report difficulty connecting to the wireless network from the other side of the building; however they have no issues when Ihey are near the antenna Which of the following is MOST likely the cause?
A technician is implementing a new wireless network to serve guests at a local office. The network needs to provide Internet access but disallow associated stations from communicating with each other. Which of the following would BEST accomplish this requirement?
A technician is deploying a low-density wireless network and is contending with multiple types of building materials. Which of the following wireless frequencies would allow for the LEAST signal attenuation?
A network administrator needs to implement an HDMI over IP solution. Which of the following will the network administrator MOST likely use to ensure smooth video delivery?
During the security audit of a financial firm the Chief Executive Officer (CEO) questions why there are three employees who perform very distinct functions on the server. There is an administrator for creating users another for assigning the users lo groups and a third who is the only administrator to perform file rights assignment Which of the following mitigation techniques is being applied'
A network technician was troubleshooting an issue for a user who was being directed to cloned websites that were stealing credentials. The URLs were correct for the websites but an incorrect IP address was revealed when the technician used ping on the user's PC After checking the is setting, the technician found the DNS server address was incorrect Which of the following describes the issue?
Which of the following services can provide data storage, hardware options, and scalability to a third-party company that cannot afford new devices?
A technician is troubleshooting a previously encountered issue. Which of the following should the technician reference to find what solution was implemented to resolve the issue?
A network requirement calls for segmenting departments into different networks. The campus network is set up with users of each department in multiple buildings. Which of the following should be configured to keep the design simple and efficient?
A technician is configuring a network switch to be used in a publicly accessible location. Which of the following should the technician configure on the switch to prevent unintended connections?
An organization wants to implement a method of centrally managing logins to network services. Which of the following protocols should the organization use to allow for authentication, authorization and auditing?
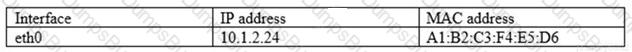
The following instructions were published about the proper network configuration for a videoconferencing device:
"Configure a valid static RFC1918 address for your network. Check the option to use a connection over NAT."
Which of the following is a valid IP address configuration for the device?
A Chief Information Officer (CIO) wants to improve the availability of a company's SQL database Which of the following technologies should be utilized to achieve maximum availability?
A technician wants to install a WAP in the center of a room that provides service in a radius surrounding a radio. Which of the following antenna types should the AP utilize?
Which of the following is a system that is installed directly on a server's hardware and abstracts the hardware from any guest machines?
A user tries to ping 192.168.1.100 from the command prompt on the 192.168.2.101 network but gets the following response: U.U.U.U. Which of the following needs to be configured for these networks to reach each other?
A network administrator is setting up several loT devices on a new VLAN and wants to accomplish the following
1. Reduce manual configuration on each system
2. Assign a specific IP address to each system
3. Allow devices to move to different switchports on the same VLAN
Which of the following should the network administrator do to accomplish these requirements?
A network administrator wants to analyze attacks directed toward the company's network. Which of the following must the network administrator implement to assist in this goal?
Which of the following is MOST commonly used to address CVEs on network equipment and/or operating systems?
A SaaS provider has decided to leave an unpatched VM available via a public DMZ port. With which of the following concepts is this technique MOST closely associated?
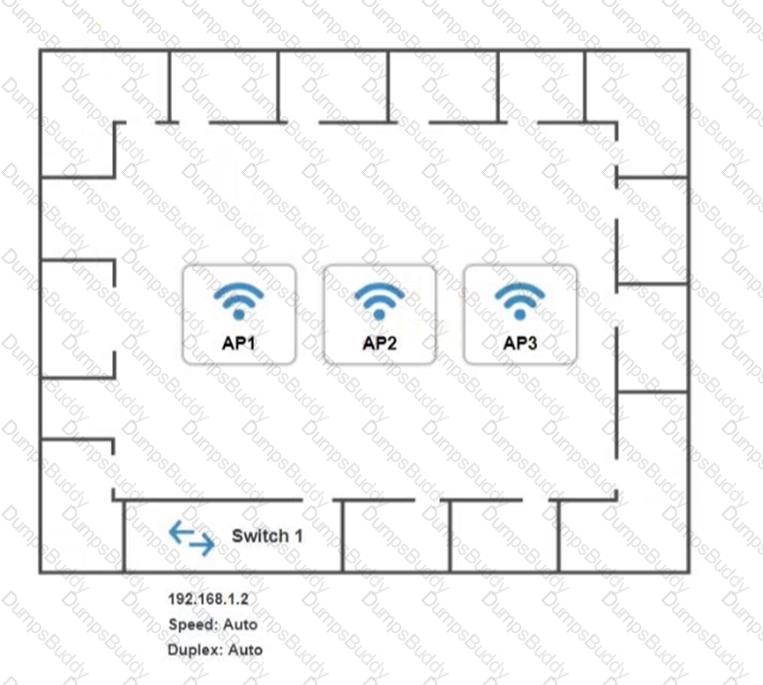
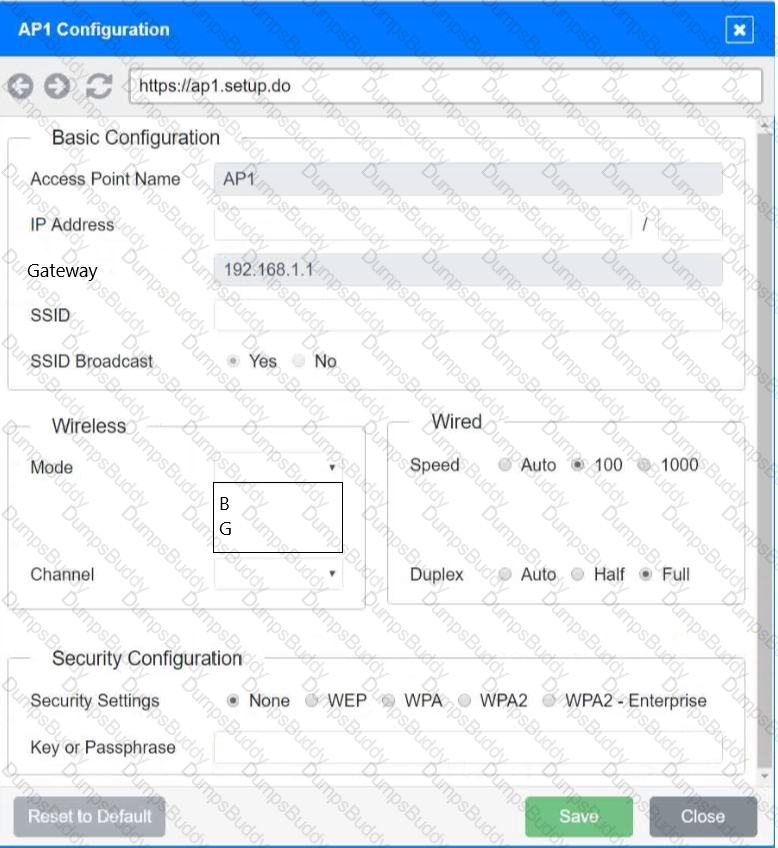
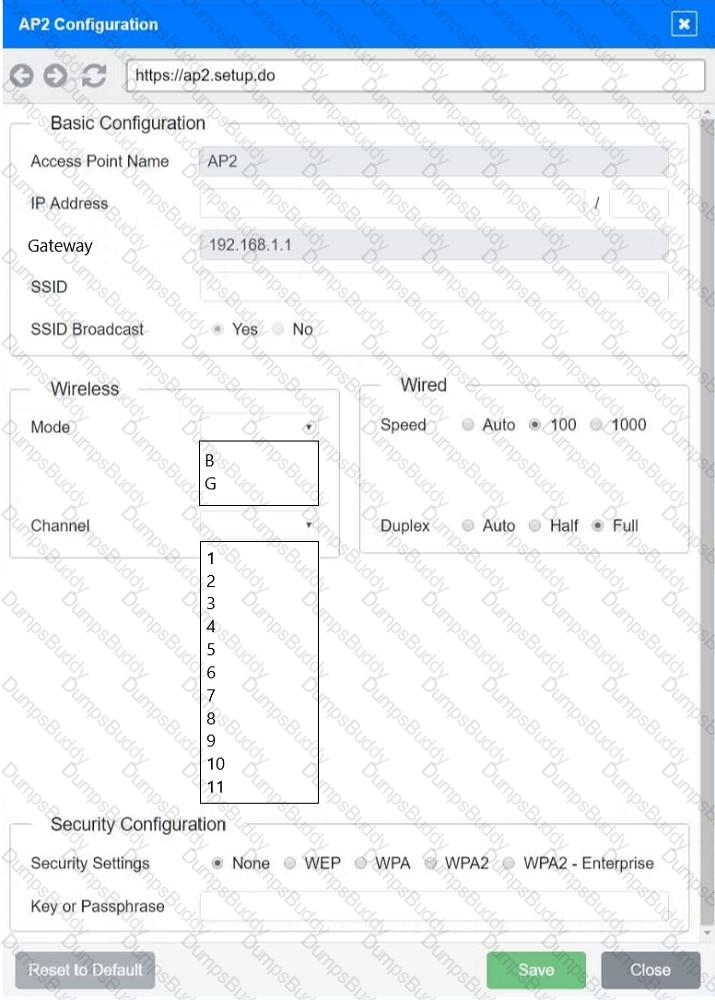
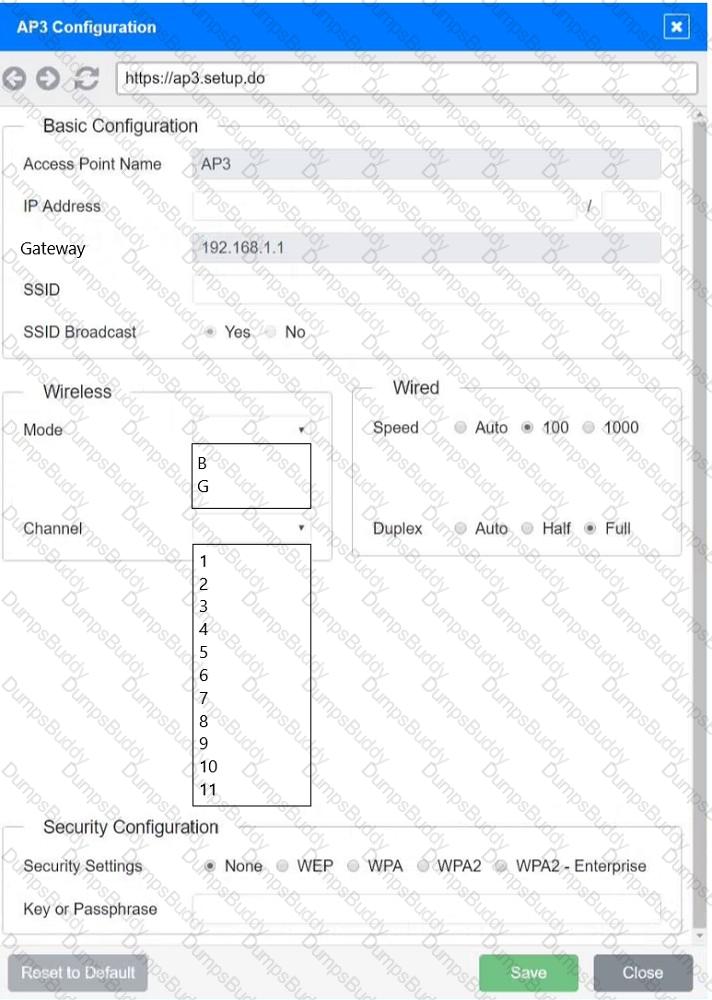
SIMULATION
You have been tasked with setting up a wireless network in an office. The network will consist of 3 Access Points and a single switch. The network must meet the following parameters:
The SSIDs need to be configured as CorpNet with a key of S3cr3t!
The wireless signals should not interfere with each other
The subnet the Access Points and switch are on should only support 30 devices maximum
The Access Points should be configured to only support TKIP clients at a maximum speed
INSTRUCTONS
Click on the wireless devices and review their information and adjust the settings of the access points to meet the given requirements.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
A network administrator has been directed to present the network alerts from the past week to the company's executive staff. Which of the following will provide the BEST collection and presentation of this data?
A network administrator needs to query the NSs for a remote application. Which of the following commands would BEST help the administrator accomplish this task?
After the A record of a public website was updated, some visitors were unable to access the website. Which of the following should be adjusted to address the issue?
A network technician is installing new software on a Windows-based server in a different geographical location. Which of the following would be BEST for the technician to use to perform this task?
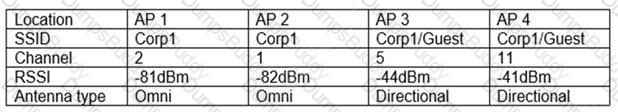
Given the following information:
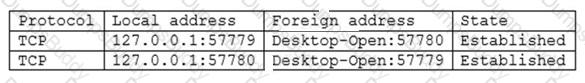
Which of the following command-line tools would generate this output?
A new cabling certification is being requested every time a network technician rebuilds one end of a Cat 6 (vendor-certified) cable to create a crossover connection that is used to connect switches. Which of the following would address this issue by allowing the use of the original cable?
A technician is installing multiple UPS units in a major retail store. The technician is required to keep track of all changes to new and old equipment. Which of the following will allow the technician to record these changes?
Which of the following factors should be considered when evaluating a firewall to protect a datacenter’s east-west traffic?
A company hired a technician to find all the devices connected within a network. Which of the following software tools would BEST assist the technician in completing this task?
A technician is troubleshooting a wireless connectivity issue in a small office located in a high-rise building. Several APs are mounted in this office. The users report that the network connections frequently disconnect and reconnect throughout the day. Which of the following is the MOST likely cause of this issue?
A technician is assisting a user who cannot connect to a network resource. The technician first checks for a link light. According to troubleshooting methodology, this is an example of:
A technician is installing a high-density wireless network and wants to use an available frequency that supports the maximum number of channels to reduce interference. Which of the following standard 802.11 frequency ranges should the technician look for while reviewing WAP specifications?
A technician is writing documentation regarding a company’s server farm. The technician needs to confirm the server name for all Linux servers. Which of the following commands should the technician run?
The management team needs to ensure unnecessary modifications to the corporate network are not permitted and version control is maintained. Which of the following documents would BEST support this?
A network technician is reviewing the interface counters on a router interface. The technician is attempting to confirm a cable issue. Given the following information:
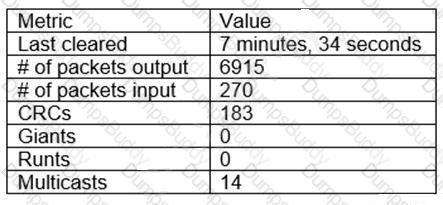
Which of the following metrics confirms there is a cabling issue?
A company is being acquired by a large corporation. As part of the acquisition process, the company's address should now redirect clients to the corporate organization page. Which of the following DNS records needs to be created?
A company requires a disaster recovery site to have equipment ready to go in the event of a disaster at its main datacenter. The company does not have the budget to mirror all the live data to the disaster recovery site. Which of the following concepts should the company select?
An IT organization needs to optimize speeds for global content distribution and wants to reduce latency in high-density user locations. Which of the following technologies BEST meets the organization’s requirements?
An engineer notices some late collisions on a half-duplex link. The engineer verifies that the devices on both ends of the connection are configured for half duplex. Which of the following is the MOST likely cause of this issue?
A technician is installing a new fiber connection to a network device in a datacenter. The connection from the device to the switch also traverses a patch panel connection. The chain of connections is in the following order:
Device
LC/LC patch cable
Patch panel
Cross-connect fiber cable
Patch panel
LC/LC patch cable
Switch
The connection is not working. The technician has changed both patch cables with known working patch cables. The device had been tested and was working properly before being installed. Which of the following is the MOST likely cause of the issue?
Which of the following service models would MOST likely be used to replace on-premises servers with a cloud solution?
A network administrator walks into a datacenter and notices an unknown person is following closely. The administrator stops and directs the person to the security desk. Which of the following attacks did the network administrator prevent?
A branch of a company recently switched to a new ISP. The network engineer was given a new IP range to assign. The ISP assigned 196.26.4.0/26, and the branch gateway router now has the following configurations on the interface that peers to the ISP:
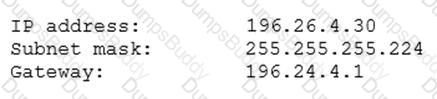
The network engineer observes that all users have lost Internet connectivity. Which of the following describes the issue?
A fiber link connecting two campus networks is broken. Which of the following tools should an engineer use to detect the exact break point of the fiber link?
Which of the following technologies provides a failover mechanism for the default gateway?
A technician is troubleshooting a network switch that seems to stop responding to requests intermittently whenever the logging level is set for debugging. Which of the following metrics should the technician check to begin troubleshooting the issue?
A technician is deploying a new switch model and would like to add it to the existing network monitoring software. The technician wants to know what metrics can be gathered from a given switch. Which of the following should the technician utilize for the switch?
Which of the following is used to track and document various types of known vulnerabilities?
Which of the following routing protocols is used to exchange route information between public autonomous systems?
A client recently added 100 users who are using VMs. All users have since reported slow or unresponsive desktops. Reports show minimal network congestion, zero packet loss, and acceptable packet delay. Which of the following metrics will MOST accurately show the underlying performance issues? (Choose two.)
Which of the following provides redundancy on a file server to ensure the server is still connected to a LAN even in the event of a port failure on a switch?
A workstation is configured with the following network details:
Software on the workstation needs to send a query to the local subnet broadcast address. To which of the following addresses should the software be configured to send the query?
A store owner would like to have secure wireless access available for both business equipment and patron use. Which of the following features should be configured to allow different wireless access through the same equipment?
Which of the following can be used to centrally manage credentials for various types of administrative privileges on configured network devices?
A technician wants to deploy a new wireless network that comprises 30 WAPs installed throughout a three-story office building. All the APs will broadcast the same SSID for client access. Which of the following BEST describes this deployment?
According to troubleshooting methodology, which of the following should the technician do NEXT after determining the most likely probable cause of an issue?
A network is experiencing a number of CRC errors during normal network communication. At which of the following layers of the OSI model will the administrator MOST likely start to troubleshoot?
Which of the following would need to be configured to ensure a device with a specific MAC address is always assigned the same IP address from DHCP?
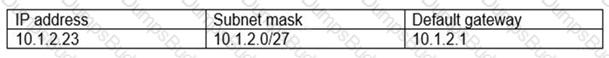
You are tasked with verifying the following requirements are met in order to ensure network security.
Requirements:
Datacenter
Ensure network is subnetted to allow all devices to communicate properly while minimizing address space usage
Provide a dedicated server to resolve IP addresses and hostnames correctly and handle port 53 traffic
Building A
Ensure network is subnetted to allow all devices to communicate properly while minimizing address space usage
Provide devices to support 5 additional different office users
Add an additional mobile user
Replace the Telnet server with a more secure solution
Screened subnet
Ensure network is subnetted to allow all devices to communicate properly while minimizing address space usage
Provide a server to handle external 80/443 traffic
Provide a server to handle port 20/21 traffic
INSTRUCTIONS
Drag and drop objects onto the appropriate locations. Objects can be used multiple times and not all placeholders need to be filled.
Available objects are located in both the Servers and Devices tabs of the Drag & Drop menu.
If at any time you would like to bring back the initial state of the simulation, please click the Reset All button.
At which of the following OSI model layers would a technician find an IP header?
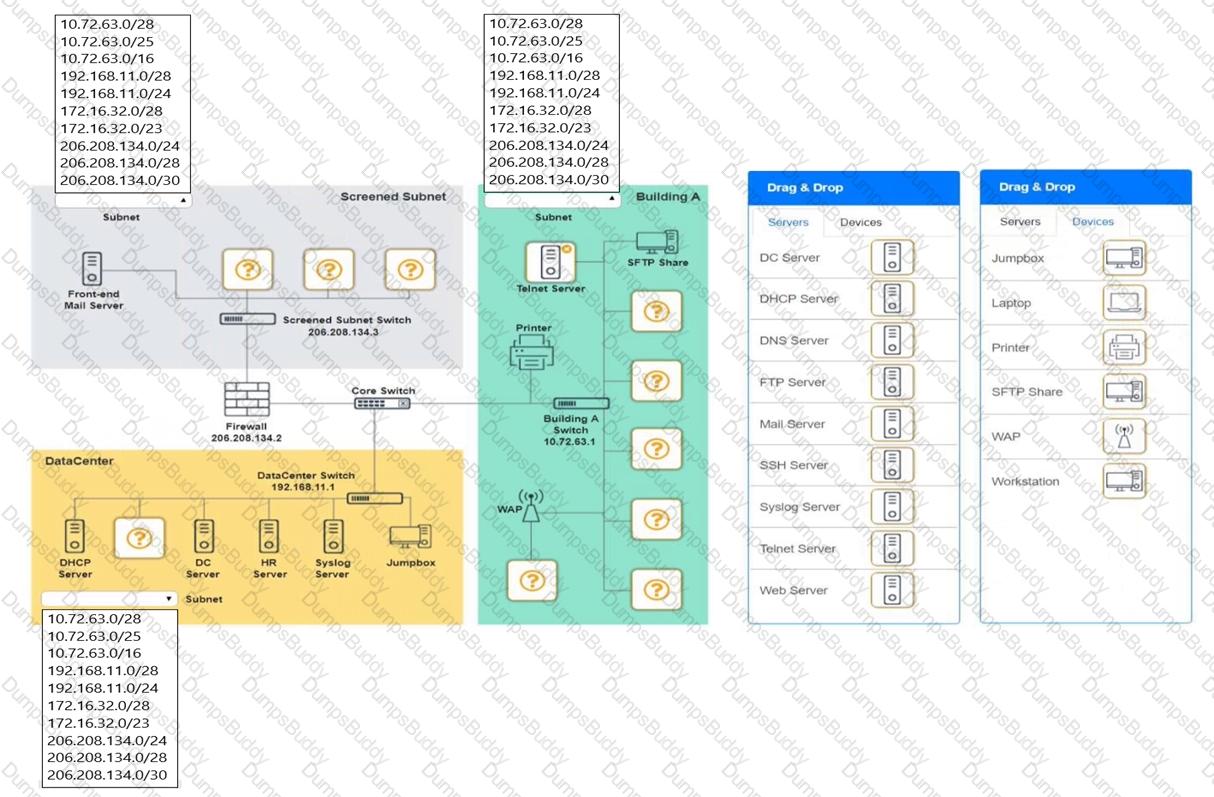
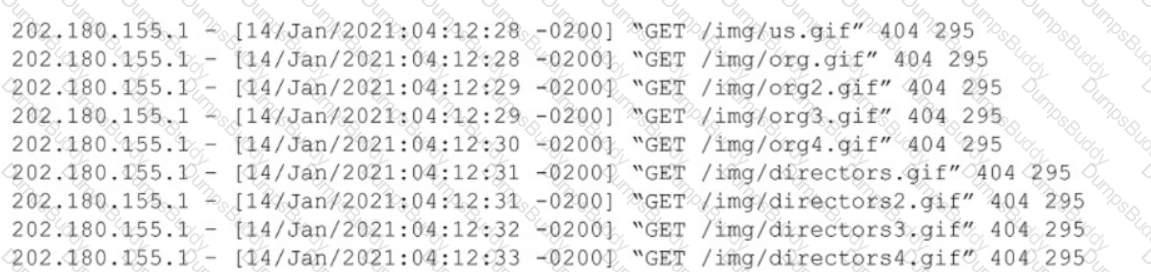
Several WIFI users are reporting the inability to connect to the network. WLAN users on the guest network are able to access all network resources without any performance issues. The following table summarizes the findings after a site survey of the area in question:
Which of the following should a wireless technician do NEXT to troubleshoot this issue?
A network administrator is designing a new datacenter in a different region that will need to communicate to the old datacenter with a secure connection. Which of the following access methods would provide the BEST security for this new datacenter?
A network engineer configured new firewalls with the correct configuration to be deployed to each remote branch. Unneeded services were disabled, and all firewall rules were applied successfully. Which of the following should the network engineer perform NEXT to ensure all the firewalls are hardened successfully?
Which of the following systems would MOST likely be found in a screened subnet?
Client devices cannot enter a network, and the network administrator determines the DHCP scope is exhausted. The administrator wants to avoid creating a new DHCP pool. Which of the following can the administrator perform to resolve the issue?
An IT director is setting up new disaster and HA policies for a company. Limited downtime is critical to operations. To meet corporate requirements, the director set up two different datacenters across the country that will stay current on data and applications. In the event of an outage, the company can immediately switch from one datacenter to another. Which of the following does this BEST describe?
A systems administrator needs to improve WiFi performance in a densely populated office tower and use the latest standard. There is a mix of devices that use 2.4 GHz and 5 GHz. Which of the following should the systems administrator select to meet this requirement?
An IDS was installed behind the edge firewall after a network was breached. The network was then breached again even though the IDS logged the attack. Which of the following should be used in place of these devices to prevent future attacks?
A technician needs to configure a Linux computer for network monitoring. The technician has the following information:
Linux computer details:
Switch mirror port details:
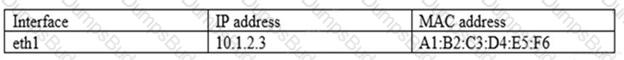
After connecting the Linux computer to the mirror port on the switch, which of the following commands should the technician run on the Linux computer?
Access to a datacenter should be individually recorded by a card reader even when multiple employees enter the facility at the same time. Which of the following allows the enforcement of this policy?
A technician receives feedback that some users are experiencing high amounts of jitter while using the wireless network. While troubleshooting the network, the technician uses the ping command with the IP address of the default gateway and verifies large variations in latency. The technician thinks the issue may be interference from other networks and non-802.11 devices. Which of the following tools should the technician use to troubleshoot the issue?
Branch users are experiencing issues with videoconferencing. Which of the following will the company MOST likely configure to improve performance for these applications?
A technician is installing a cable modem in a SOHO. Which of the following cable types will the technician MOST likely use to connect a modem to the ISP?
A network engineer performs the following tasks to increase server bandwidth:
Connects two network cables from the server to a switch stack
Configure LACP on the switchports
Verifies the correct configurations on the switch interfaces
Which of the following needs to be configured on the server?
A network administrator redesigned the positioning of the APs to create adjacent areas of wireless coverage. After project validation, some users still report poor connectivity when their devices maintain an association to a distanced AP. Which of the following should the network administrator check FIRST?
An engineer is configuring redundant network links between switches. Which of the following should the engineer enable to prevent network stability issues?
Which of the following BEST describes a network appliance that warns of unapproved devices that are accessing the network?
A technician is searching for a device that is connected to the network and has the device’s physical network address. Which of the following should the technician review on the switch to locate the device’s network port?
Wireless users are reporting intermittent internet connectivity. Connectivity is restored when the users disconnect and reconnect, utilizing the web authentication process each time. The network administrator can see the devices connected to the APs at all times. Which of the following steps will MOST likely determine the cause of the issue?
A network engineer is investigating reports of poor network performance. Upon reviewing a report, the engineer finds that jitter at the office is greater than 10ms on the only WAN connection available. Which of the following would be MOST affected by this statistic?
A technician is connecting multiple switches to create a large network for a new office. The switches are unmanaged Layer 2 switches with multiple connections between each pair. The network is experiencing an extreme amount of latency. Which of the following is MOST likely occurring?
A network administrator is installing a wireless network at a client’s office. Which of the following IEEE 802.11 standards would be BEST to use for multiple simultaneous client access?
Which of the following is used to prioritize Internet usage per application and per user on the network?
The network administrator is informed that a user’s email password is frequently hacked by brute-force programs. Which of the following policies should the network administrator implements to BEST mitigate this issue? (Choose two.)
A network administrator discovers that users in an adjacent building are connecting to the company’s guest wireless network to download inappropriate material. Which of the following can the administrator do to MOST easily mitigate this issue?
A website administrator is concerned the company’s static website could be defaced by hacktivists or used as a pivot point to attack internal systems. Which of the following should a network security administrator recommend to assist with detecting these activities?
A network technician is manually configuring the network settings for a new device and is told the network block is 192.168.0.0/20. Which of the following subnets should the technician use?
Which of the following is MOST likely to generate significant East-West traffic in a datacenter?
A network device is configured to send critical events to a syslog server; however, the following alerts are not being received:
Severity 5 LINK-UPDOWN: Interface 1/1, changed state to down
Severity 5 LINK-UPDOWN: Interface 1/3, changed state to down
Which of the following describes the reason why the events are not being received?
The following configuration is applied to a DHCP server connected to a VPN concentrator:

There are 300 non-concurrent sales representatives who log in for one hour a day to upload reports, and 252 of these representatives are able to connect to the VPN without any Issues. The remaining sales representatives cannot connect to the VPN over the course of the day. Which of the following can be done to resolve the issue without utilizing additional resources?
Which of the following would MOST likely be used to review previous upgrades to a system?
An attacker is attempting to find the password to a network by inputting common words and phrases in plaintext to the password prompt. Which of the following attack types BEST describes this action?
A user reports being unable to access network resources after making some changes in the office. Which of the following should a network technician do FIRST?
A network technician needs to ensure outside users are unable to telnet into any of the servers at the datacenter. Which of the following ports should be blocked when checking firewall configuration?
Which of the following types of devices can provide content filtering and threat protection, and manage multiple IPSec site-to-site connections?
A network technician is working at a new office location and needs to connect one laptop to another to transfer files. The laptops are newer models and do not have Ethernet ports. Access points are not available either. Which Of the following types Of wireless network SSIDs does the network technician need to configure to be able to connect the laptops together?
A network administrator is testing performance improvements by configuring channel bonding on an 802.Hac AP. Although a site survey detected the majority of the 5GHz frequency spectrum was idle, being used only by the company's WLAN and a nearby government radio system, the AP is not allowing the administrator to manually configure a large portion of the 5GHz frequency range. Which of the following would be BEST to configure for the WLAN being tested?
Which of the following would be used to adjust resources dynamically for a virtual web server under variable loads?
A user notifies a network administrator about losing access to a remote file server. The network administrator is able to ping the server and verifies the current firewall rules do not block access to the network fileshare. Which of the following tools would help identify which ports are open on the remote file server?
Which of the following would MOST likely be used to review disaster recovery information for a system?
A network administrator is decommissioning a server. Which of the following will the network administrator MOST likely consult?
While waking from the parking lot lo an access-controlled door an employee sees an authorized user open the door. Then the employee notices that another person catches the door before It closes and goes inside Which of the following attacks Is taking place?
An online gaming company needs a cloud solution that will allow for more virtual resources to be deployed when tournaments are held. The number of users who access the service
increases during tournaments. The company also needs the resources to return to baseline levels once the resources are not needed in order to reduce cost. Which of the following
cloud concepts would provide the best solution?
A network administrator needs to monitor traffic on a specific port on a switch. Which of the following should the administrator configure to accomplish the task?
Which of the following is used when a workstation sends a DHCP broadcast to a server on another LAN?
Which of the following, in addition to a password, can be asked of a user for MFA?
Which of the following provides guidance to an employee about restricting non-business access to the company's videoconferencing solution?
A network administrator is planning to implement device monitoring to enhance network visibility. The security team requires that the solution provides authentication and encryption.
Which of the following meets these requirements?
A technician uses a badge to enter a security checkpoint on a corporate campus. An unknown individual quickly walks in behind the technician without speaking. Which of the following types of attacks did the technician experience?
A network administrator wants to test the throughput of a new metro Ethernet circuit to verify that its performance matches the requirements specified m the SLA. Which of the following would BEST help measure the throughput?
An engineer recently decided to upgrade the firmware on a router. During the upgrade, the help desk received calls about a network outage, and a critical ticket was opened. The network manager would like to create a policy to prevent this from happening in the future. Which of the following documents should the manager create?
A customer is hosting an internal database server. None of the users are able to connect to the server, even though it appears to be working properly. Which of the following is the best way to verify traffic to and from the server?
Which of the following security devices would be BEST to use to provide mechanical access control to the MDF/IDF?
A company receives a cease-and-desist order from its ISP regarding prohibited torrent activity. Which of the following should be implemented to comply with the cease-and-desist order?
Which of the following cloud components can filter inbound and outbound traffic between cloud resources?
Two users on a LAN establish a video call. Which of the following OSI model layers ensures the initiation coordination, and termination of the call?
Which of the following routing protocols should be implemented to create a route between a local area network and an ISP?
Which of the following functions is used to prioritize network traffic based on the type of traffic?
A Wi-Fi network was recently deployed in a new, multilevel budding. Several issues are now being reported related to latency and drops in coverage. Which of the following is the FIRST step to troubleshoot the issues?
An infrastructure company is implementing a cabling solution to connect sites on multiple continents. Which of the following cable types should the company use for this project?
While setting up a new workstation, a technician discovers that the network connection is only 100 full duplex (FD), although it is connected to a gigabit switch.
While reviewing the interface information in the switch CLI, the technician notes the port is operating at IOOFD but Shows many RX and TX errors. The technician moves the computer to another switchport and experiences the
same issues.
Which of the following is MOST likely the cause of the low data rate and port errors?
A company's data center is hosted at its corporate office to ensure greater control over the security of sensitive data. During times when there are increased workloads, some of the company’s non-sensitive data is shifted to an external cloud provider. Which of the following cloud deployment models does this describe?
A technician is working on a ticket for a user in the human resources department who received a new PC that does not connect to the internet. All users in human resources can access the
internet. The technician can ping the PC from the human resources router but not from the IT network. Which of the following is the most likely cause of the issue?
During a recent security audit, a contracted penetration tester discovered the organization uses a number of insecure protocols. Which of the following ports should be disallowed so only encrypted protocols are allowed? (Select TWO).
Which of the following connectors and terminations are required to make a Cat 6 cable that connects from a PC to a non-capable MDIX switch? (Select TWO).
Which of the following layers is where TCP/IP port numbers identify which network application is receiving the packet and where it is applied?
A network engineer is upgrading an existing edge gateway. The company currently uses a router and needs to be able to filter on all OSI layers. Which of the following should the engineer
use to upgrade the gateway?
To access production applications and data, developers must first connect remotely to a different server From there, the developers are able to access production data Which of the following does this BEST represent?
Which of the following would be the MOST likely attack used to bypass an access control vestibule?
A company is moving to a new building designed with a guest waiting area that has existing network ports. Which of the following practices would BEST secure the network?
Users are reporting performance issues when attempting to access the main fileshare server. Which of the following steps should a network administrator perform next based on the network troubleshooting methodology?
A network administrator will be running Ethernet cables through raised ceilings. Which of the following types of Ethernet cables is the safest solution?
Network users reported that a recent firmware upgrade to a firewall did not resolve the issue that prompted the upgrade. Which of the following should be performed NEXT?
A network technician is responding to an issue with a local company. To which of the following documents should the network technician refer to determine the scope of the issue?
A network attack caused a network outage by wiping the configuration and logs of the border firewall. Which of the following sources, in an investigation to determine how the firewall was compromised, can provide the MOST detailed data?
A customer wants to log in t o a vendor's server using a web browser on a laptop. Which of the following would require the LEAST configuration to allow encrypted access to the server?
A network administrator views a network pcap and sees a packet containing the following:

Which of the following are the BEST ways for the administrator to secure this type of traffic? (Select TWO).
Which of the following authentication methods requires a user to enter a password and scan a fingerprint?
A technician troubleshoots user reports about high latency while trying to access some of the web servers. Which of the following would be the best way for the technician to identify the issue?
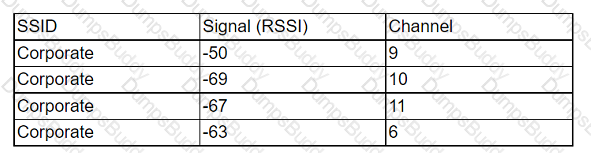
An organization has a security staff shortage and must prioritize efforts in areas where the staff will have the most impact. In particular, the focus is to
avoid expending resources on identifying non-relevant events. A security analyst is reviewing web server logs and sees the following:
Which of the following should the analyst recommend?
A network technician is investigating why a core switch is logging excessive amounts of data to the syslog server. The running configuration of the switch
showed the following logging information:
ip ssh logging events
logging level debugging
logging host 192.168.1.100
logging synchronous
Which of the following changes should the technician make to best fix the issue?
An administrator is investigating reports of network slowness in a building. While looking at the uplink interface statistics In the switch's CLI, the administrator discovers the uplink Is at 100% utilization However, the administrator is unsure how to Identify what traffic is causing the saturation. Which of the following tools should the administrator utilize to identify the source and destination addresses of the traffic?
Which of the following needs to be tested to achieve a Cat 6a certification for a company's data cawing?
An organization would like to implement a disaster recovery strategy that does not require a facility agreement or idle hardware. Which of the following strategies MOST likely meets the organization's requirements?
Which of the following is the primary function of the core layer of the three-tiered model?
An employee working in a warehouse facility is experiencing interruptions in mobile applications while walking around the facility. According to a recent site survey, the WLAN comprises autonomous APs that are directly connected to the internet, providing adequate signal coverage. Which of the following is the BEST solution to improve network stability?
A company wants to implement a disaster recovery site for non-critical applications, which can tolerate a short period of downtime. Which of the following types of sites should the company implement to achieve this goal?
A technician is troubleshooting a client's report about poor wireless performance. Using a client monitor, the technician notes the following information:
Which of the following is most likely the cause of the issue?
Which of the following is conducted frequently to maintain an updated list of a system's weaknesses?
A company has multiple offices around the world. The computer rooms in some office locations are too warm Dedicated sensors are in each room, but the process of checking each sensor takes a long time. Which of the following options can the company put In place to automate temperature readings with internal resources?
An engineer is troubleshooting poor performance on the network that occurs during work hours. Which of the following should the engineer do to improve performance?
Due to space constraints in an IDF, a network administrator can only a do a single switch to accommodate three data networks. The administrator needs a configuration that will allow each device to access its expected network without additional connections. The configuration must also allow each device to access the rest of the network. Which of the following should the administrator do to meet these requirements? (Select TWO).
An attacker targeting a large company was able to inject malicious A records into internal name resolution servers. Which of the following attack types was MOST likely used?
A customer is having issues accessing local resources on the network. A technician questions the user and discovers that a small switch had been taken out of storage and installed so that additional devices could be connected in the room. The technician runs the ping command from the PC to the network server and does not find any issues. However, data transfers to the server are slow, and the transfer appears to be locked up at times. Which of the following is the most likely cause of the issue?
A company needs to virtualize a replica of its internal physical network without changing the logical topology and the way that devices behave and are managed. Which of the following technologies meets this requirement?
After installing a series of Cat 8 keystones, a data center architect notices higher than normal interference during tests. Which of the following steps should the architect
take to troubleshoot the issue?
Which of the following attacks can be effectively protected against by using techniques to check if a connection was made by a human user? (Select two).
A new office space is being designed. The network switches are up. but no services are running yet A network engineer plugs in a laptop configured as a DHCP client to a switch Which ol the following IP addresses should be assigned to the laptop?
Which of the following policies outlines the software and hardware requirements for using personally owned devices to conduct business?
A network administrator connects two unmanaged switches together with a straight-through Ethernet cable. The administrator reviews the connection and notices that the uplinks are not on. Which of the following options offers the best solution for the issue?
A technician received a report that some users in a large, 30-floor building are having intermittent connectivity issues. Users on each floor have stable connectivity, but do not have connectivity to other floors. Which of the following devices is MOST likely causing the issue?
A network administrator is configuring a new switch and wants to connect two ports to the core switch to ensure redundancy. Which of the following configurations would meet this
requirement?
A technician installed an 8-port switch in a user's office. The user needs to add a second computer in the office, so the technician connects both PCs to the switch and connects the switch to the wall jack. However, the new PC cannot connect to network resources. The technician then observes the following:
• The new computer does not get an IP address on the client's VLAN.
• Both computers have a link light on their NICs.
• The new PC appears to be operating normally except for the network issue.
• The existing computer operates normally.
Which of the following should the technician do NEXT to address the situation?
Which of the following physical security methods Is the MOST effective to prevent tailgating?
A small office has a wireless network with several access points that are used by mobile devices. Users occasionally report that the wireless connection drops or becomes very slow. Reports confirm that this only happens when the devices are connected to the office wireless network. Which of the following is MOST likely the cause?
Network connectivity in an extensive forest reserve was achieved using fiber optics. A network fault was detected, and now the repair team needs to check the integrity of the fiber cable. Which of me following actions can reduce repair time?
A company has wireless APS that were deployed with 802.11g. A network engineer has noticed more frequent reports of wireless performance issues during the lunch hour in comparison to the rest of the day. The engineer thinks bandwidth consumption will increase while users are on their breaks, but network utilization logs do not show increased bandwidth numbers. Which Of the following would MOST likely resolve this issue?
An attacker sends more connection requests than a server can handle, causing the server to crash- Which of the following types of attacks is this an example of?
Which of the following can be used to decrease latency during periods of high utilization of a firewall?
A global company has acquired a local company. The companies are geographically separate. The IP address ranges for the two companies are as follows:
· Global company: 10.0.0.0/16
· Local company: 10.0.0.0/24
Which of the following can the network engineer do to quickly connect the two companies?
A network administrator needs to create a way to redirect a network resource that has been on the local network but is now hosted as a SaaS solution. Which of the following
records should be used to accomplish the task?
A network deployment engineer is deploying a new single-channel 10G optical connection. Which of the following optics should the engineer MOST likely use to satisfy this requirement?
A network engineer is monitoring a fiber uplink to a remote office and notes the uplink has been operating at 100% capacity for a long duration. Which of the following performance metrics is MOST likely to be impacted with sustained link saturation?
A network administrator received a report staling a critical vulnerability was detected on an application that is exposed to the internet. Which of the following Is the appropriate NEXT step?
A new global ISP needs to connect from central offices in North America to the United Kingdom. Which of the following would be the BEST cabling solution for this project?
A bank installed a new smart TV to stream online video services, but the smart TV was not able to connect to the branch Wi-Fi. The next day. a technician was able to connect the TV to the Wi-Fi, but a bank laptop lost network access at the same time. Which of the following is the MOST likely cause?
An administrator would like to create a fault-tolerant ring between three switches within a Layer 2 network. Which of the following Ethernet features should the administrator employ?
A user is having difficulty with video conferencing and is looking for assistance. Which of the following would BEST improve performance?
A company wants to implement a large number of WAPs throughout its building and allow users to be able to move around the building without dropping their connections Which of the following pieces of equipment would be able to handle this requirement?
A technician is troubleshooting a workstation's network connectivity and wants to confirm which switchport corresponds to the wall jack the PC is using Which of the following concepts would BEST help the technician?
A lab environment hosts Internet-facing web servers and other experimental machines, which technicians use for various tasks A technician installs software on one of the web servers to allow communication to the company's file server, but it is unable to connect to it Other machines in the building are able to retrieve files from the file server. Which of the following is the MOST likely reason the web server cannot retrieve the files, and what should be done to resolve the problem?
A customer wants to segregate the traffic between guests on a hypervisor. Which of the following does a technician need to configure to meet the requirement?
A network administrator decided to use SLAAC in an extensive IPv6 deployment to alleviate IP address management. The devices were properly connected into the LAN but autoconfiguration of the IP address did not occur as expected. Which of the following should the network administrator verify?
Two remote offices need to be connected securely over an untrustworthy MAN. Each office needs to access network shares at the other site. Which of the following will BEST provide this functionality?
An organization with one core and five distribution switches is transitioning from a star to a full-mesh topology Which of the following is the number of additional network connections needed?
A network technician is investigating an IP phone that does not register in the VoIP system Although it received an IP address, it did not receive the necessary DHCP options The information that is needed for the registration is distributes by the OHCP scope All other IP phones are working properly. Which of the following does the technician need to verify?
A network technician has multimode fiber optic cable available in an existing IDF. Which of the following Ethernet standards should the technician use to connect the network switch to the existing fiber?
A network engineer is designing a new secure wireless network. The engineer has been given the following requirements:
1 Must not use plaintext passwords
2 Must be certificate based
3. Must be vendor neutral
Which of the following methods should the engineer select?
A systems administrator is running a VoIP network and is experiencing jitter and high latency. Which of the following would BEST help the administrator determine the cause of these issues?
Which of the following policies is MOST commonly used for guest captive portals?